See the Moon phase expected for March 26, 2026 as well as when the next Full Moon is expected.
Blog Posts
Blog Posts
Hints and Solutions for Hurdle – March 26, 2026
Hints and answers to today’s Hurdle all in one place.
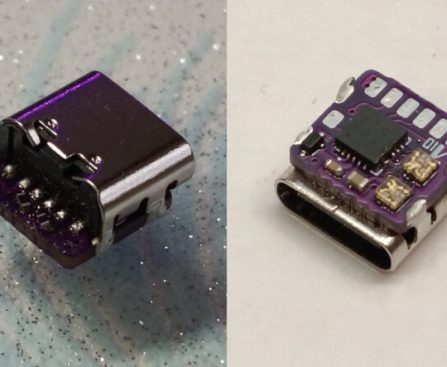
AngstromIO: Compact 9.0 x 8.9 mm ATtiny1616 Board for USB-C Connector
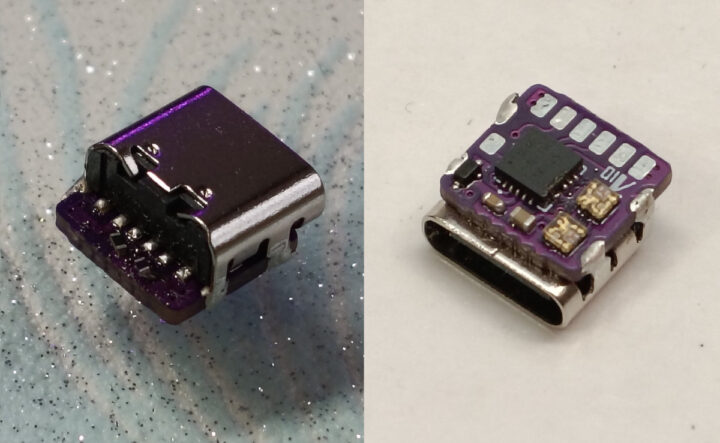
Dieu-de-l-elec’s AngstromIO is an incredibly tiny open-source development board based on Microchip’s ATtiny1616 MCU. Measuring just 9.0 x 8.9 mm, the board is barely larger than the edge-mounted USB Type-C connector that powers it, making it ideal for highly space-constrained embedded projects. Despite its tiny footprint, AngstromIO packs a QFN20-packaged ATtiny1616 MCU, two addressable SK6805-EC15 RGB LEDs, and includes access to various usable GPIOs, including I2C, UART, and UPDI for programming. AngstromIO specifications: MCU â Microchip ATtiny1616 8-bit AVR microcontroller @ up to 20 MHz with 16KB flash, 2KB SRAM, 256 bytes EEPROM USB â 1x USB Type-C port (power only, no data lines connected to the MCU) Expansion via solder pads UPDI pin for programming I2C (SDA, SCL) 2x GPIOs (PB2/TX, PA3) 5V and GND Misc â 2x SK6805-EC15 addressable RGB LEDs Power Supply 5V via USB-C port Ultra-low power consumption (down to 200nA in power-down mode) Dimensions â 9.0 […]
The post AngstromIO – A tiny 9.0 x 8.9 mm ATtiny1616 board that fits on top of a USB-C connector appeared first on CNX Software – Embedded Systems News.
Why Is OpenAI the Way It Is?
ChatGPT developer OpenAI has killed off Sora, its shortform video app. What is CEO Sam Altman planning next for the AI company?
Wordle March 26, 2026: Answer and Hints Today
Here’s the answer for “Wordle” #1741 on March 26 as well as a few hints, tips, and clues to help you solve it yourself.
Hints and Answers for NYT Strands – March 26, 2026
The NYT Strands hints and answers you need to make the most of your puzzling experience.
Today’s NYT Connections Hints: Clues & Answers for March 26, 2026
Connections is a New York Times word game that’s all about finding the “common threads between words.” How to solve the puzzle.
I’m watching the Japanese GP for free this weekend — how to live stream F1 for free
How to watch F1 for free. Live stream the Japanese GP from the 2026 F1 season for free from anywhere in the world.
The Most Predictable Chapter of the Manus Story is Unfolding Now
Did anyone think there would not be a reckoning over this tie-up?
40+ Home Deals from Amazon’s Big Spring Sale — Save on Cooling Sheets, Air Purifiers, and Top Robot Vacuums
Amazon’s Big Spring Sale has some great home deals. We spotted savings on air purifiers, carpet cleaners, cooling bedding, and more.